Bypassing Anti-Virus with Metasploit MSI Files
A while back I put together a short blog titled 10 Evil User Tricks for Bypassing Anti-Virus. The goal was to highlight common anti-virus misconfigurations. While I was chatting with Mark Beard he mentioned that I neglected to include how to use Metasploit payloads packaged in MSI files. So in this blog I’ll try to make amends by providing a quick and dirty walkthrough of how to do that. This should be useful for both sysadmins and penetration testers.
Creating MSI Files that Run Metasploit Payloads
The Metasploit Framework team (and the greater security community) has made it easy and fun to package Metasploit payloads in almost any file format. Thankfully that includes MSI files. MSI files are Windows installation packages commonly used to deploy software via GPO and other methods. Luckily for penetration testers some anti-virus solutions aren’t configured by default to scan .msi files or the .tmp files that are generated when MSI files are executed. For those of you who are interested in testing if your anti-virus solution stops Metasploit payloads packaged in .MSI files I worked with Mark to put together this short procedure.
- Use the msfconsole to create a MSI file that will execute a Metasploit payload. Feel free to choose your favorite payload, but I chose adduser because it makes for an easy test. Note: This payload requires local admin privileges to add the user.
msfconsole use payload/windows/adduser set PASS Attacker123! set USER Attacker generate -t msi -f /tmp/evil.msi
Alternatively, you can generate the MSI file with the msfvenom ruby script that comes with Metasploit:
msfvenom -p windows/adduser USER=Attacker PASS=Attacker123! -f msi > evil.msi
- Copy the evil.msi file to the target system and run the MSI installation from the command line to execute the Metasploit payload. From a penetration test perspective using the /quiet switch is handy, because it suppresses messages that would normally be displayed to the user.
msiexec /quiet /qn /I c:tempevil.msi
- Check anti-virus logs to see if the payload was identified. You can also check to see if the payload executed and added the “Attacker” user with the command below. If user information is returned then the payload executed successfully.
net user attacker
The MSI file is configured to execute the payload, but will not complete the formal installation process, because the authors (Ben Campbell and Parvez Anwar) forced it to fail using some invalid VBS. So uninstalling it won’t be required after execution. However, during execution a randomly named .tmp file will be created that contains the MSF payload in the c:windowsInstaller folder. The file should be cleaned up automatically, but if the installation fails out for any reason the file will most likely need to be removed manually. The file will look something like “c:windowsInstallerMSI5D2F.tmp”.
As a side note, it appears that the .tmp file is basically a renamed .exe file. So if you manually rename the .tmp file to an .exe file you can execute it directly. Also, once it’s renamed to an .exe file anti-virus starts to pick it up.
Escalating Privileges with MSI Packages
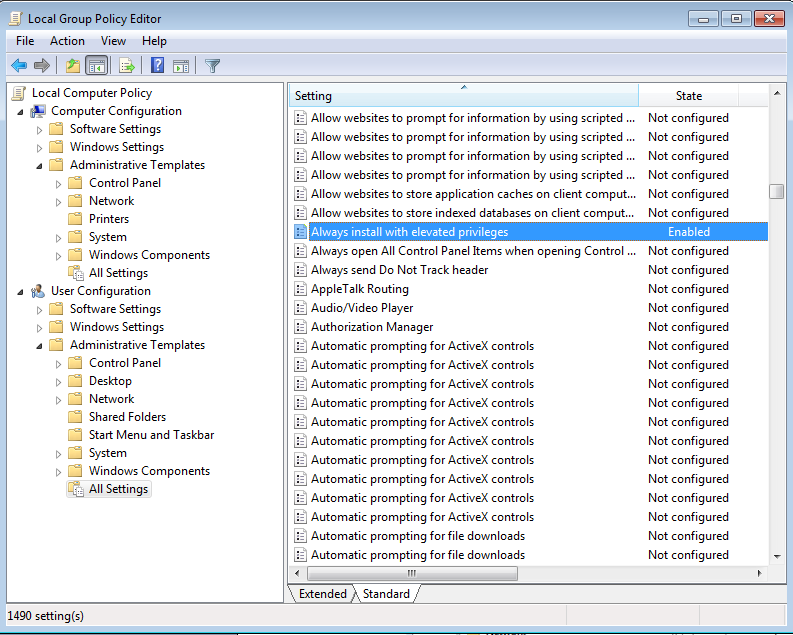
As it turns out MSI files are handy for more than simply avoiding anti-virus. Parvez Anwar figured out that they can also be used to escalate privileges from local user to local administrator if the group policy setting “Always install with elevated privileges” is enabled for the computer and user configurations. The setting is exactly what it sounds like. It provides users with the ability to install any horrible ad-ware, pron-ware, or malware they want onto corporate systems. In gpedit.msc the configuration looks something like this:
The policies can also be viewed or modified from the following registry locations:
[HKEY_CURRENT_USERSoftwarePoliciesMicrosoftWindowsInstaller]
“AlwaysInstallElevated”=dword:00000001
[HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsInstaller]
“AlwaysInstallElevated”=dword:00000001
For those of you who don’t want to go through hassle of generating and executing the MSI files manually Ben Campell (meatballs) and Parvez Anwar were nice enough to put together a Metasploit module to do it for you called “Windows AlwaysInstallElevated MSI“. The technique was also mentioned during a recent presentation by Rob Fuller (mubix) and Chris Gates (carnal0wnage) titled “AT is the new BLACK” which is worth checking out.
Wrap Up
The down side is that MSI files can pose a serious threat if anti-virus and group policy settings are not configured securely. However, the bright side is it’s an easy problem to fix in most environments. Good hunting, and don’t forget to Hack Responsibly!
References
Explore more blog posts

Navigating Cybersecurity Regulations Across Financial Services
Learn about five areas businesses should consider to help navigate cybersecurity regulations, such as the Digital Operations Resiliency Act (DORA).

A New Era of Proactive Security Begins: The Evolution of NetSPI
Introducing The NetSPI Platform, the proactive security solution used to discover, prioritize, and remediate the most important security vulnerabilities. Plus, get a first look at NetSPI’s updated brand!

Penetration Testing: What is it?
Learn about 15 types of penetration testing, how pentesting is done, and how to choose a penetration testing company.