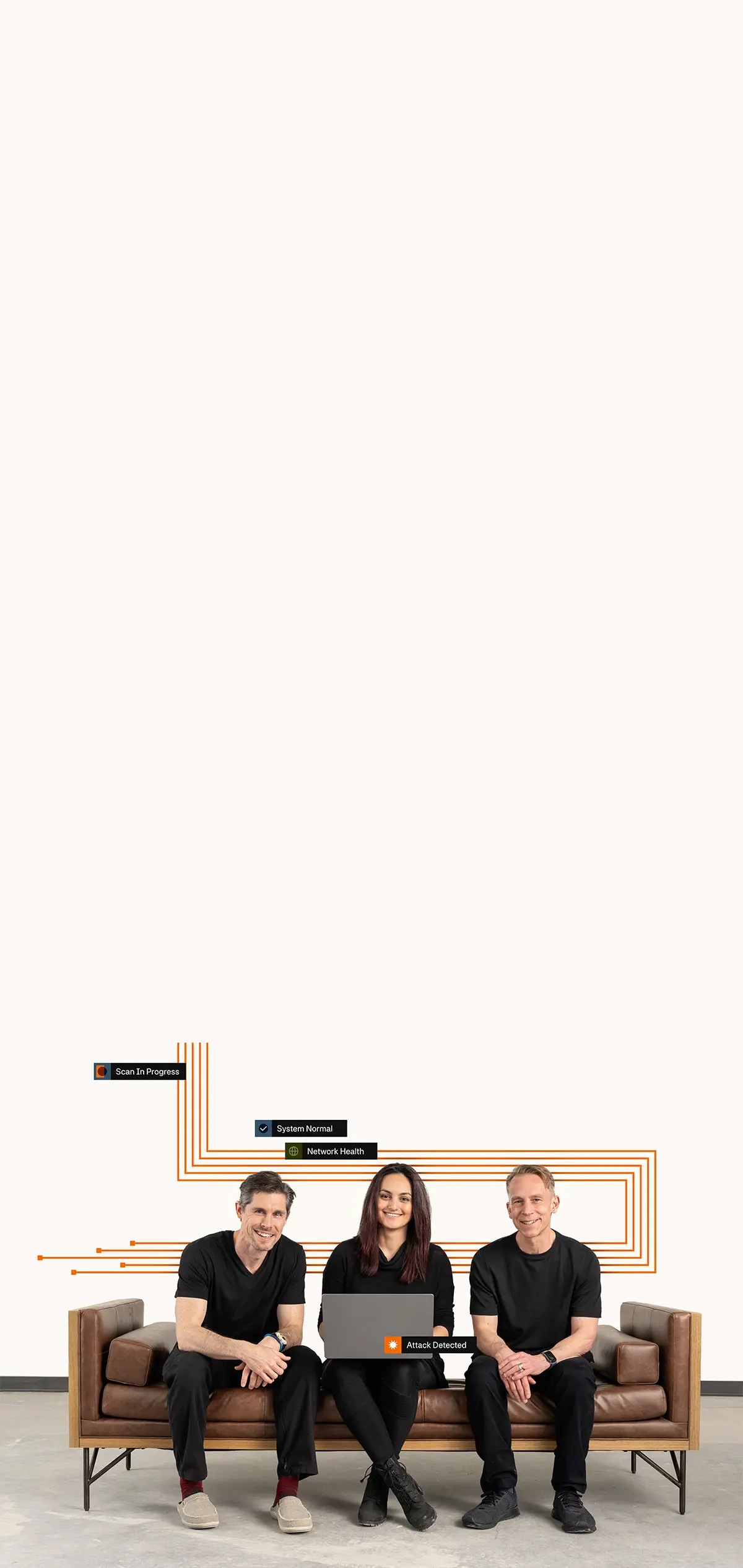
Hack Responsibly
Browse Hack Responsibly, a technical blog by The NetSPI Agents. Dive deep into the latest CVEs and vulnerabilities our team uncovers, and how we help NetSPI customers protect against the most important threats today.
Our favorite picks

15 Ways to Bypass the PowerShell Execution Policy
By default, PowerShell is configured to prevent the execution of PowerShell scripts on Windows systems. In this blog I’ll cover 15 ways to bypass the PowerShell execution policy without having local administrator rights on the system.

Four Ways to Bypass Android SSL Verification and Certificate Pinning
As pentesters, we’d like to convince the app that our certificate is valid and trusted so we can man-in-the-middle (MITM) it and modify its traffic. In this blog I’ll go through 4 techniques you can use to bypass SSL certificate checks on Android.

CVE-2024-21378 — Remote Code Execution in Microsoft Outlook
Learn how NetSPI discovered that Microsoft Outlook was vulnerable to authenticated remote code execution (RCE) via synced form objects.

Elevating Privileges with Azure Site Recovery Services
Discover how NetSPI uncovered and reported a Microsoft-managed Azure Site Recovery service vulnerability and how the finding was remediated.

Web2 Bugs in Web3 Systems
Discover how attackers use vulnerabilities in off-chain components to achieve critical impact against on-chain systems.

Azure Deployment Scripts: Assuming User-Assigned Managed Identities
Learn how to use Deployment Scripts to complete faster privilege escalation with Azure User-Assigned Managed Identities.

CVE-2024-21378 — Remote Code Execution in Microsoft Outlook
NetSPI discovered that Microsoft Outlook was vulnerable to authenticated remote code execution (RCE) via synced form objects. Learn how NetSPI discovered and exploited the vulnerability.

Extracting Sensitive Information from the Azure Batch Service
The added power and scalability of Batch Service helps users run workloads significantly faster, but misconfigurations can unintentionally expose sensitive data.
The Silk Wasm: Obfuscating HTML Smuggling with Web Assembly
A new technique for HTML smuggling using Web Assembly helped us bypass potential malware detection.

Why TOTP Won’t Cut It (And What to Consider Instead)
Time-Based One-Time Password (TOTP) is a common method for two factor authentication (2FA) but its lack of rate limiting can create security gaps.

Automating Managed Identity Token Extraction in Azure Container Registries
Learn the processes used to create a malicious Azure Container Registry task that can be used to export tokens for Managed Identities attached to an ACR.

Exploiting XPath Injection Weaknesses
Defend your web applications from XPath Injection: Explore the intricacies of this critical threat, understand its impact, and learn effective mitigation strategies.

Mistaken Identity: Extracting Managed Identity Credentials from Azure Function Apps
NetSPI explores extracting managed identity credentials from Azure Function Apps to expose sensitive data.

Abusing Entra ID Misconfigurations to Bypass MFA
While conducting an Entra Penetration Test, we discovered a simple misconfiguration in Entra ID that allowed us to bypass MFA.

A First Look at Python in Excel
How can you leverage Python in Excel for Red Team Operations? James Williams present a quick overview the new functionality and how it may be used.

